Title
Create new category
Edit page index title
Edit category
Edit link
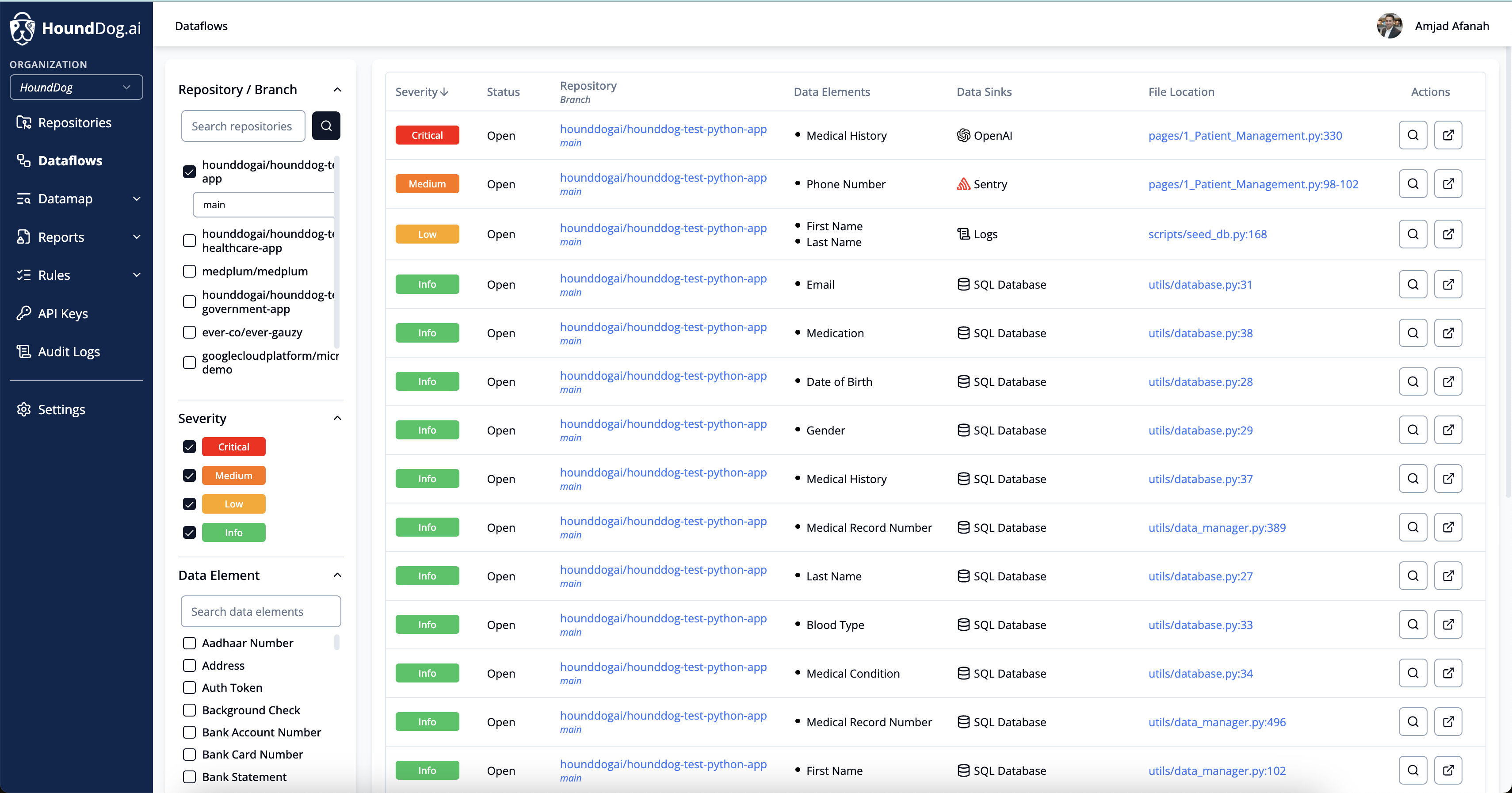
Dataflows
The Dataflows page provides a view of sensitive data flows detected by the HoundDog.ai code scanner. It shows how data moves from your applications to various data sinks, including logs, files, APIs, third party services, and AI integrations, where it may be stored or shared. This creates code level evidence of processing activities, helping you keep privacy reports such as Records of Processing Activities up to date for GDPR, CCPA, and other frameworks.
Risky data flows are rarely intentional. They tend to emerge as codebases grow. A developer may print a full user object for debugging, or a tainted variable may carry PII through multiple transformations. By the time anyone notices, the data may already be logged or sent to a third party.
Each data flow is assigned a severity level of Critical, Medium, Low, or Info. Severity is determined based on the sensitivity of the data elements involved, which can be customized in the Data Elements page, and the destination of the data, including any allowlist rules configured in the Data Sinks page.
You can explore data flows using advanced filters, including:
- Repository: the name of the scanned code repository
- Branch: the scanned branch
- Severity: the assigned severity level
- Data Elements: the types of sensitive data involved
- Data Sinks: where the data is exposed
- Status: the current state, such as open, closed, or ignored
To investigate further, click on any row to drill down into the details of a specific data flow.
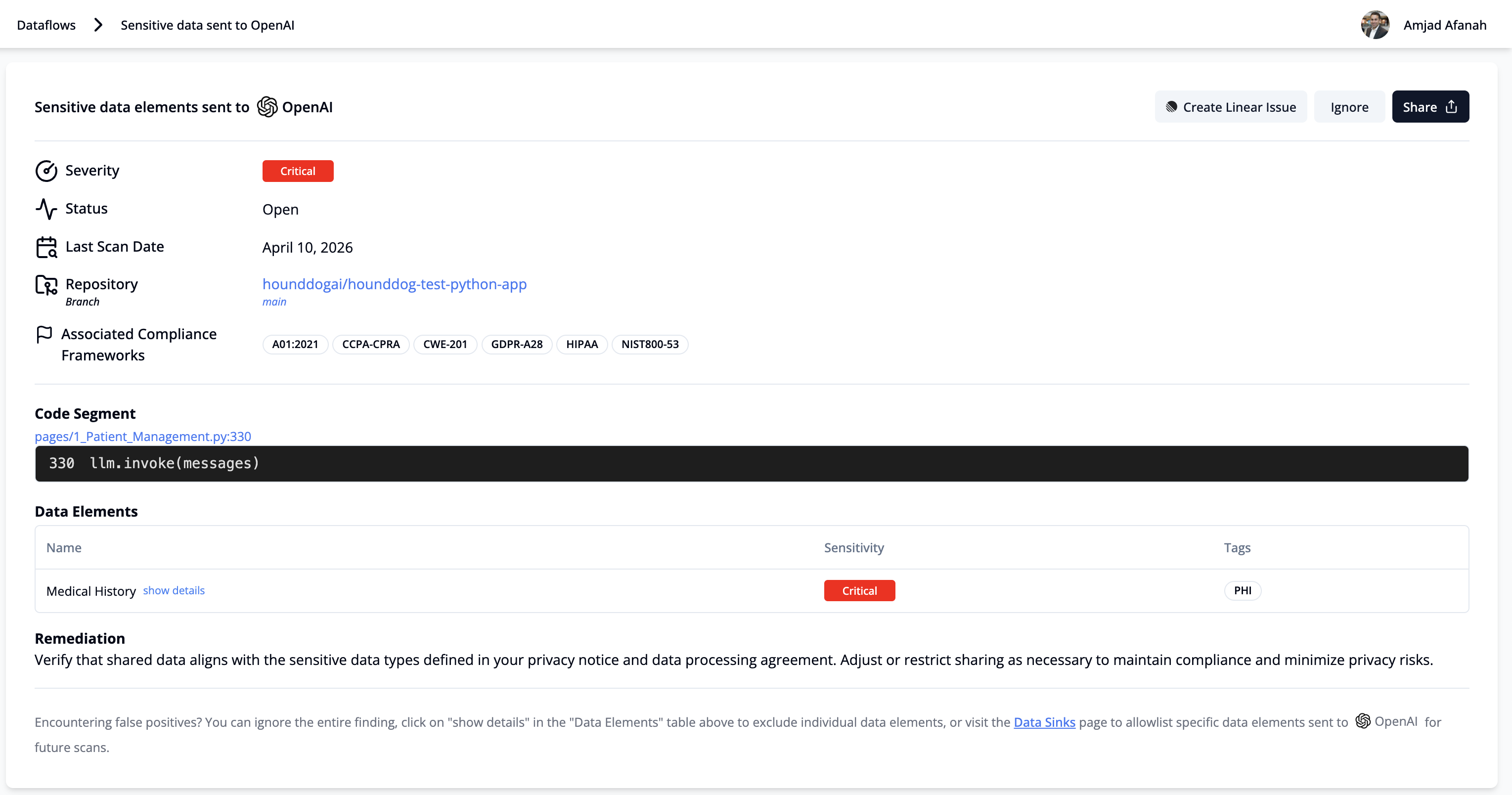
The dataflow drill-down page allows you to view granular details about the data flow, including:
- Severity
- Status
- Last Scan Date
- Repository and Branch Details
- Associate Compliance Frameworks (e.g. CCPA, GDPR, HIPAA, NIST800-53)
- Storage Medium or Third-Party Integration Where Sensitive Data Is Exposed
- File URL
- Code Segment
- Remediation Guidelines
- Data Elements Detected
Lastly, there are three actions that can be taken on this page:
- File Jira or Linear Ticket: You will need to configure Jira or Linear on the Settings page to take advantage of this feature.
- Ignore this data flow: This will change the status from Open to Ignored.
- Ignore individual data elements: If a data element (e.g., username) is falsely flagged, you can ignore that specific data element, while the unignored ones will continue to appear. The severity of the issues will then be adjusted based on the sensitivity of the remaining unignored data elements.
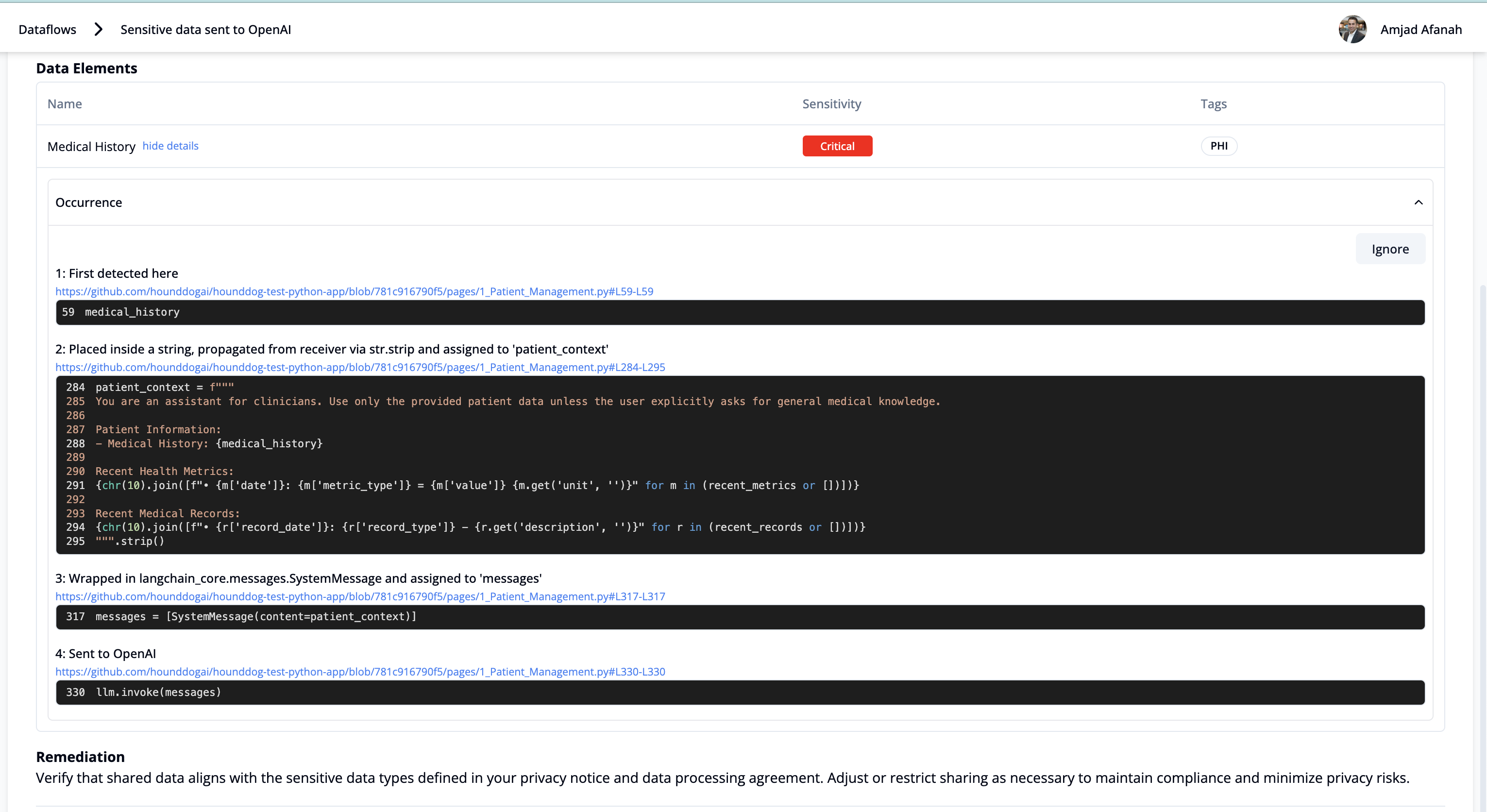
- View a detailed data flow trace: For each exposed data element, you can click "Show Details" to see a full trace of all transformations, including how tainted variables flow across files, that ultimately led to the sensitive data being exposed in the risky data sink.
© 2025 HoundDog.ai, Inc. All rights reserved.