Title
Create new category
Edit page index title
Edit category
Edit link
Overview
What is HoundDog.ai?
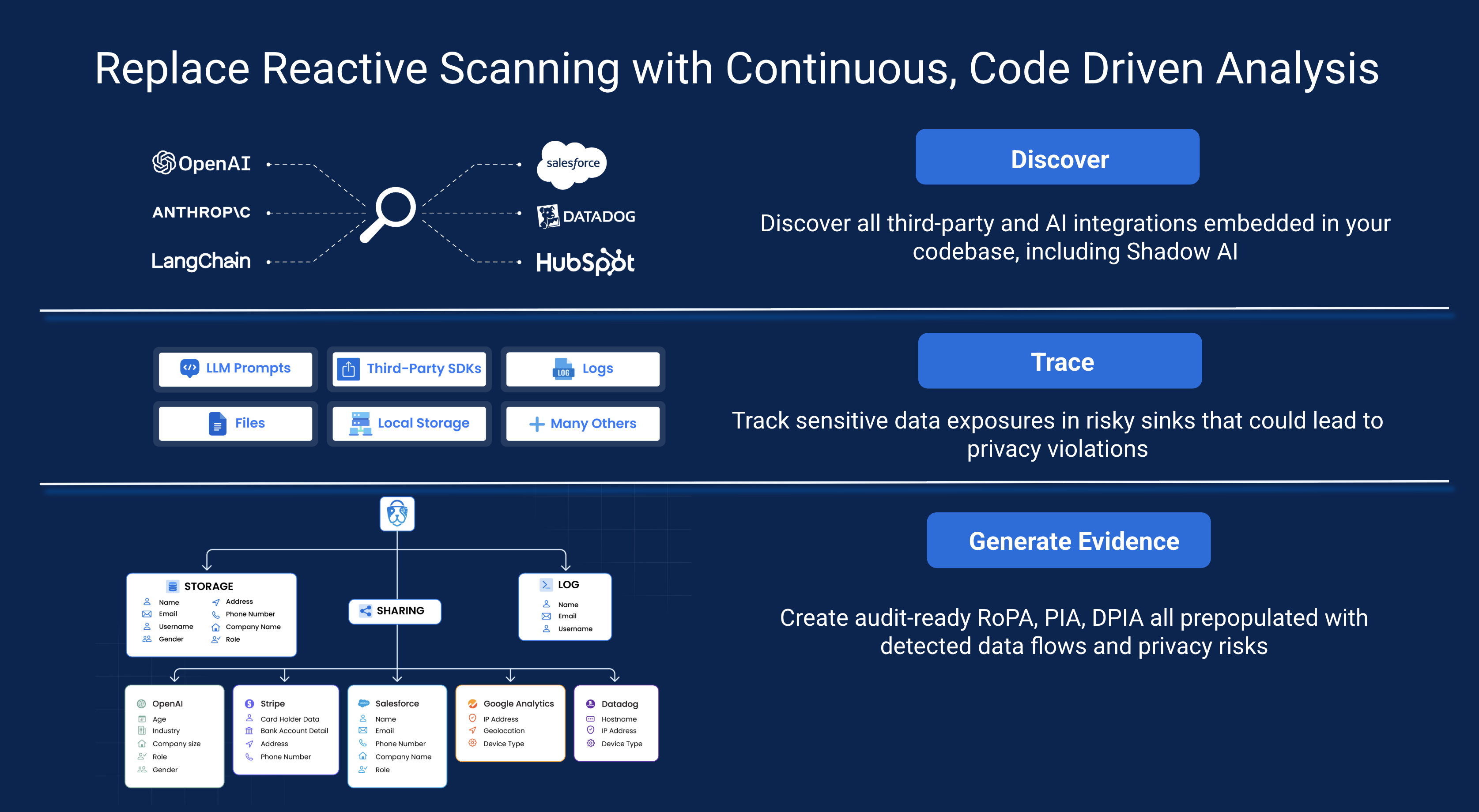
HoundDog.ai’s lightweight, modern privacy code scanner enables technology driven companies to embed privacy into the development process, catch privacy risks early, and automate GDPR data mapping and privacy reporting (RoPA, PIA, and DPIA). The scanner replaces the guesswork in data flow mapping with code level evidence, mapping sensitive data flows directly from your applications’ source code, including across logs, APIs, SDKs, and AI integrations, before anything reaches production.
Many teams use it to prevent overlogging of sensitive data such as PII, PHI, CHD, and authentication tokens (see the full list of supported data elements). It also helps uncover hidden third party and AI integrations (see the full list of supported data sinks) and detect data flow changes that can violate internal policies or data processing agreements due to silent code updates early in development. Common issues include simple oversights such as printing full user objects or passing tainted variables.
HoundDog.ai’s lightweight, high performance code scanner is designed to track sensitive data flows across complex transformations and interpolations in code. These risks are often introduced by developers or AI generated code, where tainted variables or accidental dumping of objects can occur. The scanner applies deep interprocedural and taint analysis across files and functions to accurately trace how sensitive data propagates through applications and identify potential exposures before they reach production.
HoundDog.ai is trusted by Fortune 1000 companies in the technology and healthcare sectors and has recently integrated with Replit to bring privacy code scanning to its 45M creators, offering instant visibility into sensitive data flows and privacy issues.
The platform enables organizations to:
🧭 Step 1: Discover AI and third-party integrations
- Track with high confidence the types of AI and third party integrations that developers have embedded in their code repositories as part of your AI governance and third party risk management efforts.
🔐 Step 2: Trace sensitive data flows
- Track over 100 sensitive data types, including PII, PHI, CHD and authentication tokens. Follow them through transformations such as tainted variables across file boundaries, no matter how deeply buried, down to risky sinks such as LLM prompts, logs, temporary files, local storage, and third-party SDKs.
⚖️ Step 3: Bake in your privacy standards
- Apply allowlists to define which data types are permitted in LLM prompts and other risky sinks. Automatically block unsafe pull requests to maintain compliance with Data Processing Agreements.
📑 Step 4: Build customer trust through transparent data handling
- Generate evidence-based data maps that show where sensitive data is collected, processed and shared, including through AI and third-party integrations.
- Produce audit-ready Records of Processing Activities (RoPA) and Privacy Impact Assessments (PIAs), pre-populated with detected data flows and privacy risks aligned with GDPR, CCPA, HIPAA, and other regulatory frameworks.
Free vs Paid Plans
For details on what is included in the free version and the paid plans, please visit our GitHub repository or pricing page for the most up to date information.
How is it different?
- 100% Complementary: Our goal is not to replace CodeQL, Semgrep, Snyk, Checkmarx, or similar tools, but to fill the gap left by reactive privacy platforms that scan data only after it reaches production. These tools often miss shadow AI and third party integrations in code and cannot keep pace with development speed, leaving privacy teams to waste cycles backfilling data flows. Traditional SAST scanners also fall short since they focus on security vulnerabilities, not privacy risks. HoundDog.ai fills this gap as the best in class solution for sensitive data leak prevention and privacy compliance automation, with broad coverage of CWE-201, CWE-209, CWE-312, CWE-313, CWE-315, CWE-532, CWE-539. For a detailed comparison, see our GitHub repository. Checkmarx has also highlighted our integration as essential for catching PII leaks before code reaches production - see details.
- Privacy-Focused: Our static code scanner is purposely built to map sensitive data flows across all storage mediums as well as third party and AI integrations embedded in code. This reduces data mapping overhead by up to 90% and minimizes sensitive data leaks in logs and other risky mediums to nearly zero.
- Blazingly Fast with a Tiny Footprint: Written in Rust - a language renowned for its performance, memory safety, and portability - HoundDog.ai's code scanner can process 1 million lines of code in under a minute. The unzipped binary is less than 30MB in size, making it super lightweight with minimal impact on your workflows.
- Highly Accurate: We maintain a meticulously curated set of rules and definitions covering multiple domains (e.g., PII, PHI, PIFI) out of the box, prioritizing the elimination of false positives. These rules are enhanced through AI workflows, reviewed by human experts, and tested against real-world scenarios.
Contact
If you need any help or would like to send us feedback, please shoot us an email at [email protected].
© 2025 HoundDog.ai, Inc. All rights reserved.